IPFire, an open-source firewall and router platform, has introduced a new feature called Domain Block List (DBL) that allows users to block malicious domains using community-driven updates. This system relies on contributions from users worldwide to identify and report harmful websites, making it easier to protect networks from threats like malware, phishing, and unwanted ads. The DBL works by maintaining a list of known bad domains, which IPFire automatically blocks when detected in traffic. This update aims to improve security while reducing the burden on administrators who manage firewall rules manually.
The traditional approach to domain blocking in firewalls often requires administrators to manually update lists of blocked domains. This process can be time-consuming and error-prone, especially when new threats emerge. IPFire’s new DBL system changes this by enabling real-time updates through a community-driven model. Users can submit domains they believe are malicious, and after verification, these domains are added to the central DBL database. This ensures that the list remains current without requiring users to manually track threats themselves.
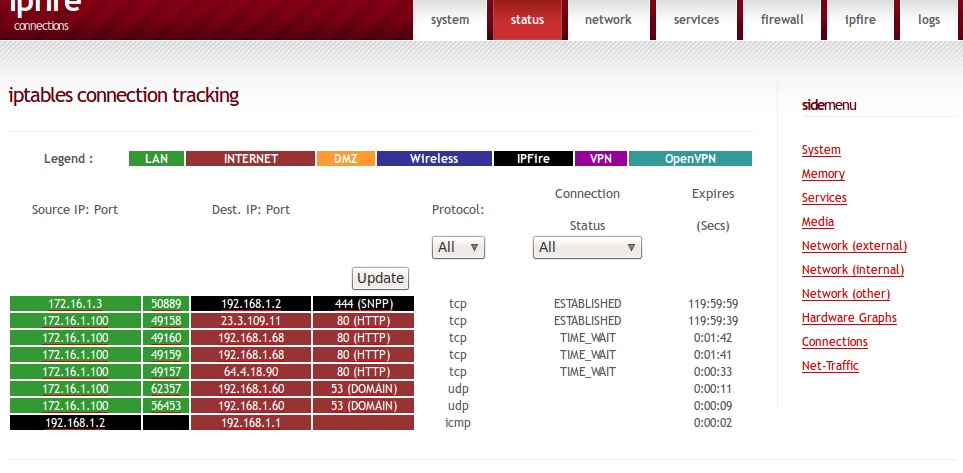
The DBL system is integrated into IPFire’s core firewall features. When a device connects to the internet through an IPFire gateway, the firewall checks all incoming and outgoing traffic against the DBL. If a domain matches an entry in the list, the connection is blocked. This process happens quickly, with minimal impact on network performance. The system also includes tools for users to review blocked domains, check for false positives, and submit feedback to the community. This feedback loop helps improve the accuracy of the DBL over time.
One of the key advantages of the community-driven model is its ability to scale. Traditional domain block lists are often limited by the resources of a single organization, which can lead to outdated or incomplete data. In contrast, IPFire’s DBL grows as more users contribute information. This collective effort ensures that even niche or emerging threats are identified and blocked promptly. For example, if a new phishing site is discovered by a user in Europe, that domain is added to the DBL and automatically blocked for users in Asia, Africa, and elsewhere within hours.
The DBL also supports advanced filtering options. Users can choose to block specific categories of domains, such as those associated with malware distribution, adult content, or cryptocurrency scams. These categories are managed through the community’s input, with users voting on which domains should be included in each category. This system allows for more precise blocking while reducing the risk of accidentally blocking legitimate websites. Security researchers and network administrators have praised the DBL for its potential to reduce the workload of managing firewall rules.
IPFire has also taken steps to ensure the reliability of the DBL. Before a domain is added to the list, it undergoes a verification process to confirm its malicious nature. This includes checking the domain against known threat databases and analyzing its behavior. Users can also flag domains that they believe are falsely blocked, which are then reviewed by the community. This dual-layer verification system helps maintain the accuracy of the DBL while minimizing disruptions to legitimate traffic.
The DBL is available to all IPFire users, regardless of their technical expertise. New users can enable the feature through the IPFire web interface, which provides step-by-step guidance on how to configure the DBL. For advanced users, the system offers deeper customization options, such as creating custom blocklists or integrating the DBL with third-party security tools. Looking ahead, IPFire plans to expand the DBL’s capabilities to include support for blocking domains based on geographic location, user behavior patterns, or machine learning models.
Website: https://www.ipfire.org/

