Recovering a lost Windows password can feel impossible, but tools like Windows Password Decryptor exist to help. These programs are designed for legitimate users who forgot their passwords, not for hacking. They work by scanning the Windows registry for stored password hashes and attempting to match them with common passwords or dictionary words. While they can be effective for basic passwords, they have limits and require specific setup steps. Here’s how they function and what you need to know before using them.
Windows Password Decryptor is a third-party tool that targets the SAM (Security Accounts Manager) database, where Windows stores user passwords. The tool uses a dictionary attack method, which means it tries thousands of common passwords from pre-built lists to find a match. This approach works best for simple passwords but fails against complex ones with numbers, symbols, or random characters. The tool does not use brute-force methods (which try every possible combination) because that would take too long. Instead, it relies on precompiled wordlists and user input to guess the password quickly.
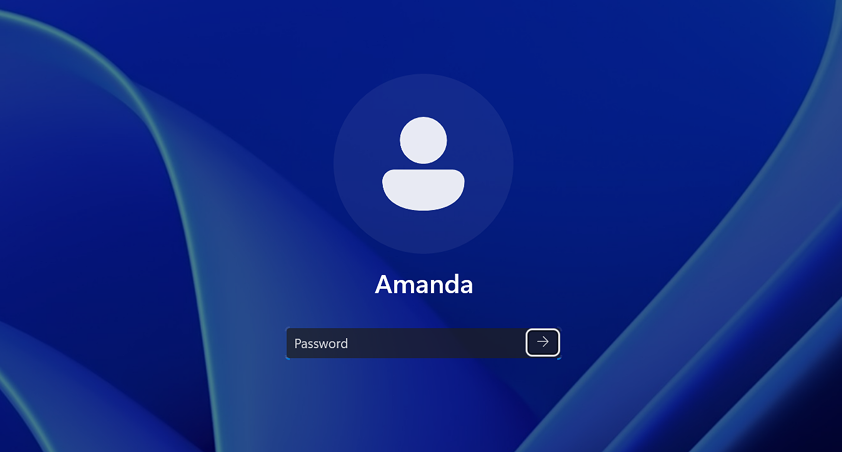
To use the tool, you must create a bootable USB drive or CD with the software. This requires a working computer to prepare the media and then access the locked Windows system. When you boot from the USB, the tool loads into a temporary environment and scans the SAM database for user accounts. It then attempts to decrypt the password hashes using its dictionary. If a match is found, the tool displays the password, allowing you to log in. However, if the password isn’t in the dictionary, the tool cannot recover it, and you’ll need alternative methods like resetting the password through Microsoft’s account recovery process or using a password reset disk.
The tool is compatible with Windows 7, 8, 10, and 11 but requires .NET Framework 4.5 to run. It works only on local systems and cannot access passwords stored on remote servers or networked machines. Additionally, it cannot bypass BitLocker encryption unless the recovery key is available. For users who need to recover passwords for others (e.g., family members or employees), the tool can be useful, but it must be used ethically and legally. Unauthorized access to another person’s account is illegal in most jurisdictions.
One limitation of dictionary attacks is that they depend on the quality of the wordlist. If the user’s password isn’t in the list, the tool fails. To improve success rates, some tools allow users to add custom passwords to the dictionary. However, this requires prior knowledge of the password’s structure or common patterns. For example, if the password includes a person’s name or birthdate, the tool might guess it if those details are in the wordlist. Still, this method is not foolproof and works best for weak or predictable passwords.
Another important consideration is the physical access requirement. The tool needs direct access to the computer’s hardware to create the bootable media and run the decryption process. This means it won’t work for remote systems or devices that are locked out of the BIOS/UEFI settings. Additionally, if the user has enabled a BIOS password or Secure Boot, the tool may not boot properly. In such cases, the user might need to disable these security features temporarily, which could pose risks if not done correctly.
For users who rely on Windows for business or personal use, having a password recovery plan is crucial. This includes creating a password reset disk, enabling Microsoft account recovery options, or using a password manager to store credentials securely. While tools like Windows Password Decryptor can be helpful in emergencies, they are not a substitute for proactive password management. Strong passwords, two-factor authentication, and regular backups are far more effective for long-term security.
If you’re considering using this tool, ensure you have legal permission to access the system. Unauthorized use could lead to serious consequences, including legal action. Always follow the tool’s instructions carefully and back up important data before attempting any recovery process. If the password is particularly complex or the tool fails, consult a professional IT service or contact Microsoft support for further assistance. Remember, while password recovery tools can be useful, they are not a guarantee of success and should be used as a last resort.

