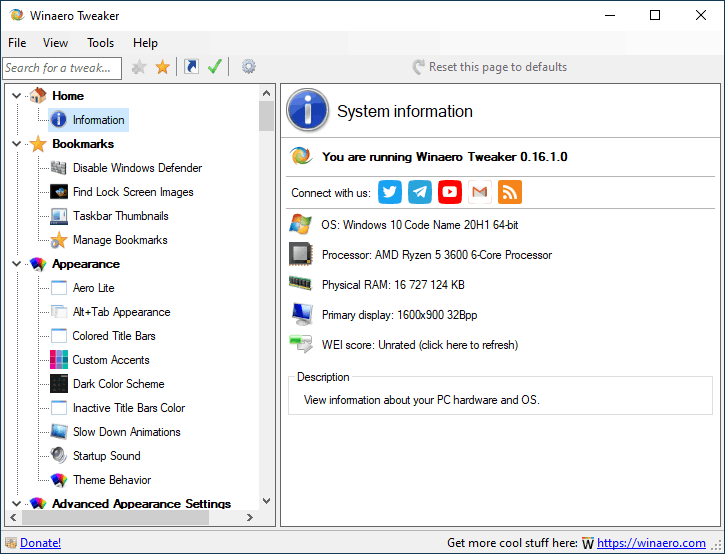
Ever used a program to make Windows look and work a little different? Maybe change the colors, or how the taskbar looks? Winaero Tweaker is a popular tool for doing just that. But recently, lots of people have been surprised to see Microsoft Defender, the security program on Windows, flagging Winaero Tweaker as a dangerous threat – a Trojan! This is a case of what’s called a ‘false positive,’ and it’s a bit confusing. Let’s break down what’s happening and why you probably don’t need to panic.
What’s a Trojan, Anyway?
First, let’s understand what a Trojan is. A Trojan horse (or just ‘Trojan’) is a type of malware – short for malicious software – that disguises itself as something harmless. Think of the original Trojan horse from Greek mythology: it looked like a gift, but it was full of soldiers ready to attack. Computer Trojans do the same thing. They might pretend to be a game, a useful tool, or even a system update. Once you run it, it can do sneaky things like steal your passwords, give hackers access to your computer, or install other nasty programs. Microsoft Defender is designed to find and block these threats.
Why is Defender Flagging Winaero Tweaker?
So, why is Defender suddenly seeing Winaero Tweaker as a Trojan? It all comes down to how Defender works. Defender uses something called ‘heuristic analysis.’ This means it doesn’t just look for known viruses (those it already has a signature for). Instead, it analyzes the behavior of programs. If a program does things that look suspicious – like modifying system files, accessing sensitive areas of the operating system, or trying to hide itself – Defender might flag it as potentially malicious, even if it’s not actually a virus.
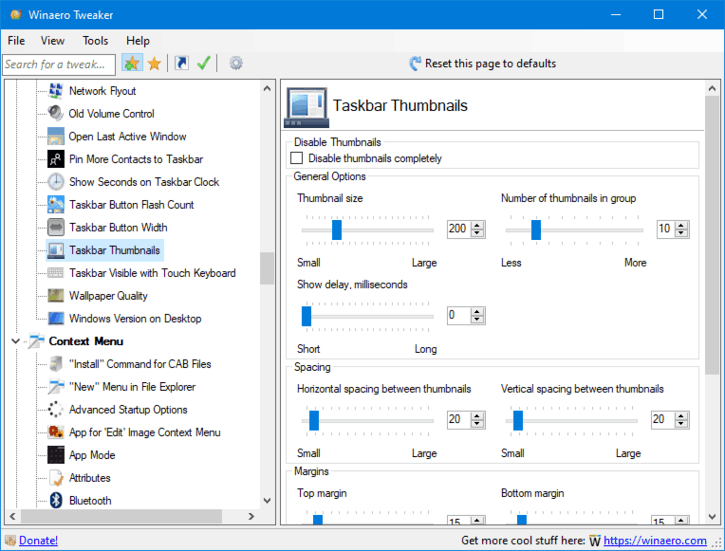
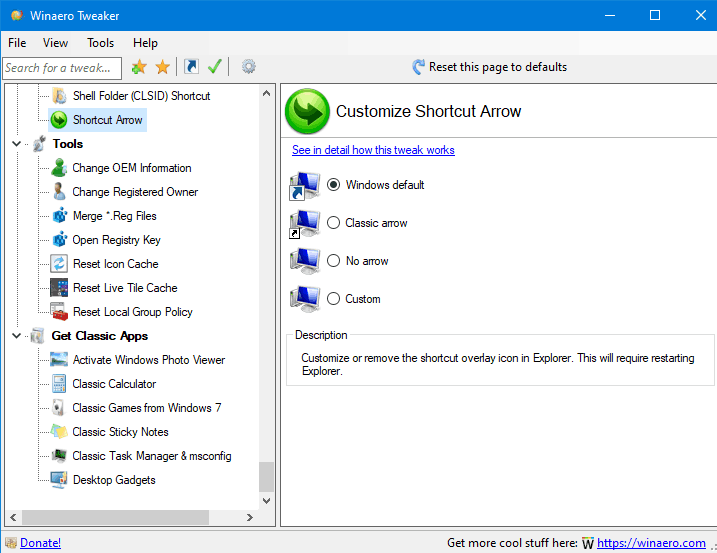
Winaero Tweaker, by its very nature, does modify system files and access sensitive areas. That’s how it changes the way Windows works! It’s designed to tweak settings that are normally hidden or difficult to change. This behavior, unfortunately, triggers Defender’s heuristic analysis and raises a red flag. Defender is essentially saying, “Hey, this program is doing things that look like a Trojan might do!”
False Positives: When Defender Makes a Mistake
A ‘false positive’ is when a security program incorrectly identifies a safe program as a threat. It’s like a security guard stopping someone who looks suspicious but turns out to be completely innocent. False positives happen all the time with antivirus software. They’re a necessary evil – it’s better to be cautious and flag something as potentially dangerous than to miss a real threat.
In the case of Winaero Tweaker, it’s almost certainly a false positive. Winaero Tweaker is a legitimate program developed by a reputable developer, Dmitry Matveev. He’s been creating Windows utilities for years, and his software is generally considered safe and trustworthy. Many experienced Windows users rely on Winaero Tweaker to customize their systems.
Microsoft’s Response and What’s Being Done
Microsoft is aware of the issue and is working to correct it. They’ve acknowledged that Winaero Tweaker is a false positive and are in the process of updating their Defender definitions to stop flagging it. This process takes time, as Microsoft needs to carefully analyze the program and ensure that the change won’t allow actual malware to slip through.
In the meantime, Dmitry Matveev has also been working on solutions. He’s been analyzing Defender’s reports to understand exactly what behavior is triggering the flags and making adjustments to his program to reduce the likelihood of false positives, without compromising its functionality. He’s also providing information to Microsoft to help them understand that Winaero Tweaker is safe.
Why This Happens – The Challenge of Tweaking Windows
This situation highlights a fundamental challenge in Windows security. Windows is a complex operating system with many hidden settings and low-level functions. Programs that modify these settings – like Winaero Tweaker – are inherently going to trigger security warnings. It’s a balancing act between allowing users to customize their systems and protecting them from malicious software. Antivirus programs need to be sensitive enough to detect real threats but not so sensitive that they flag legitimate tools as dangerous.
What Should You Do?
If you’re using Winaero Tweaker and Defender is flagging it, here’s what you can do:
- Don’t Panic: It’s almost certainly a false positive.
- Temporarily Disable Defender’s Real-time Protection (Not Recommended Long-Term): This will allow you to use Winaero Tweaker, but it leaves your computer vulnerable to real threats. Only do this if you’re absolutely sure you trust the source of Winaero Tweaker (i.e., download it directly from the official Winaero website: https://winaero.com/).
- Exclude Winaero Tweaker from Defender Scans: This is the recommended approach. You can tell Defender to ignore Winaero Tweaker during scans. To do this:
- Open Windows Security.
- Go to ‘Virus & threat protection.’
- Click ‘Manage settings’ under ‘Virus & threat protection settings.’
- Scroll down to ‘Exclusions’ and click ‘Add or remove exclusions.’
- Click ‘Add an exclusion’ and choose ‘File’ to exclude the Winaero Tweaker executable file (usually
WinaeroTweaker.exe).
- Keep Defender Updated: Make sure you have the latest Defender definitions installed. Microsoft is working on a fix, and updates will include the correction.
- Download from Official Source: Always download Winaero Tweaker from the official Winaero website to avoid getting a fake or malicious version.
This incident with Winaero Tweaker is a good reminder that antivirus software isn’t perfect. False positives happen, and it’s important to understand why they happen and how to deal with them. It also highlights the importance of downloading software from trusted sources and being cautious about running programs that modify system files. While tweaking your Windows experience can be fun, always prioritize your computer’s security.

